Passwords are the keys to our privacy. They keep prying eyes out of our social media accounts, financial institutions, and even our business lives. But how do you know if your passwords are actually protecting you? After all, the statistics don’t lie: you have likely experienced a data breach and never knew it! So, if you’re rightly worried about a data breach, where can you learn how to keep your passwords safe?
Read on to learn more about why your passwords are at risk, and what systems help keep them safe.
First Things First: A Majority of Americans Have Been Part of a Data Breach
It sounds crazy, but it’s true – not only have over 60 percent of Americans had their information leaked, the average American has their data breached approximately four times per year. The full scope of these breaches is impossible to measure, but it can be devastating on a personal or commercial level. If someone gains access to your financial institution accounts, they can sell your information, steal your identity, or even funnel money straight out of your accounts.
Even accounts you may consider less critical than your financial ones can be used to exploit you or those you know. A stolen social media account is a common tool for phishing attempts. If they message your entire list of Facebook friends from your account, most of those contacts are more likely to click malicious links that eventually steal their data too. When thinking of why and how to keep your passwords safe, this is just one thing to think about – a vulnerable password quickly spirals into even more risk.
Is Your Stolen Password a “Skeleton Key” for Your Life?
You may be thinking “So what that my social media password was breached?” After all, many of these stolen accounts are ones that you don’t use anymore, don’t care about, or can’t affect your life in any significant way. But a data breach is much more dangerous than you think because the information gathered doesn’t exist in a vacuum.
Think about this: have you ever used the same password on more than one website? Of course you have! 65 percent of people admit to using the same password for more than one account. And many of these people probably use the same password for almost all of their accounts.
That means your password security for everything you have an account for is kept only as safe as the weakest link. And there are plenty of websites out there that collect your information without putting a moment’s thought into keeping that information safe.
Your stolen social media account could be a master key for criminals to access all of your online accounts: your online banks, your private email, and beyond.
How to Keep Your Passwords Safe
Now that you understand the risk of a vulnerable password, it’s time to look into the solutions that can prevent a data breach or minimize the risk of a data breach that is outside your control.
Use a Password Manager
If there were a single way to solve your password problems, it’s a password manager. While no solution is fool-proof, a password manager eliminates or greatly reduces the biggest risks associated with account intrusion. Using a password manager offers you:
Safe Storage for Passwords
Especially in business settings, storing passwords can be the weak link that leaves your accounts vulnerable. Shared spreadsheets that make rounds through emails or get saved on desktops at the office or on a workaholic’s home PC make it easy for a small slip up to turn into a complete breach of your company’s passwords. Even worse – many employees still rely on things like a sticky note to remember critical system passwords.
A reputable password manager gives you a single place to store your passwords and it’s designed to keep them secure. Techferno, for example, adds extra layers of security to ensure the user accessing the account is you. Even if someone steals your password, if they try to access your account from a different device, they have to supply an additional passphrase to gain access.
Of course, there’s several deep layers of technical security too – such as end-to-end encryption and host-proof hosting – stacked on top that you should consider a necessity for any password manager worth trusting.
Your passwords in a secure password manager are not only are harder for hackers to intentionally access, they’re harder for you to accidentally share. You can’t send your password manager account to the wrong email like you could an Excel document, and you can’t accidentally have a sticky note password show up in a Facebook post when your social media manager is sharing an in-office event.
Easy Creation of Better Passwords
One of the simplest concepts in password security is also one of the hardest ones in practice: creating strong passwords. One of the easiest ways for someone to access your account is if you chose a password that’s common or easy to guess. There are thousands of passwords that you may think are clever, but they’re frequently used by people all over the world. Terms like “opensesame”, “password123”, or “qwerty” are as effective as trying to keep a door shut with a paperclip.
But creating strong passwords isn’t easy. That’s because there’s two core ideas behind a strong password, and both are challenging:
#1. Non-Word Passwords – Any password that uses dictionary words is inherently weaker than a random jumble of characters, assuming they’re of the same length. Quality password managers will provide you with tools that generate these types of random strings, that will look like “x9@.#E41U%*f” or similar.
#2. Long Passwords – The second, and more effective strategy, is creating long passwords. While most websites require passwords of just eight characters, you’re better off producing a password that’s 20 characters. This is because every additional character included in your password adds an exponential amount of processing time required for password cracking tools to eventually “try” the password you created.
In addition to creating these longer passwords, your password manager lets you quickly access, copy, and paste them when you need them. So even if your password is 100 characters long, it won’t be up to you to remember it.
Reduce the Need for Reusing Passwords
Lastly, and perhaps most importantly, a password manager gives you the ability to easily create and track unique passwords for every account you make. Why does this matter? A password that’s reused on several accounts dramatically increases your chance of having every account breached when just one of those websites fails at securing your information.
Many of the credential leaks that you hear about on the “dark web” are just dumps of poorly secured passwords on websites that didn’t put any effort into keeping your data safe. If you use the same password for your bank account that you do for any other software, the security of your bank’s website doesn’t matter. If the other account is involved in a password leak, online criminal groups share your login data and will try using it on all major websites like banks or government websites.
When your password manager generates strong passwords, keeps track of them, and lets you access them quickly, you can make a unique password for every platform without it interrupting how easily you can access those accounts.
Understand Phishing Risks
The second key aspect of how to keep your passwords safe is to understand the threats lurking across the web. Fortunately, with email and online services becoming ubiquitous across our personal and commercial lives, most people are at least vaguely familiar with the key issues to watch. However, it’s still important to know that new tricks and variations of old ones arise every day.
What Is Phishing?
The simple definition of phishing is the use of deception to capture information that you would otherwise never share. Phishing is typically done through impersonal communication like emails, instant messages, or now even in text. The goal of the “phisher” is to get your guard down and have you share the information willingly, which circumvents any type of security you may otherwise have.
What Are Common Types of Phishing Attacks?
Phishing is a catch-all term with a lot of nuance underneath. But all phishing attacks have one thing in common: they count on you not asking too many questions. The most likely phishing attacks you are to experience are:
Email Phishing
Often just referred to simply as phishing, this is where it all started. Email phishing attempts will reach out to your business or personal email pretending to be someone they’re not. Sometimes they represent themselves as a business offering you something for free. Most email phishing these days include deceptive domains or spoofed email addresses that make them look legitimate.
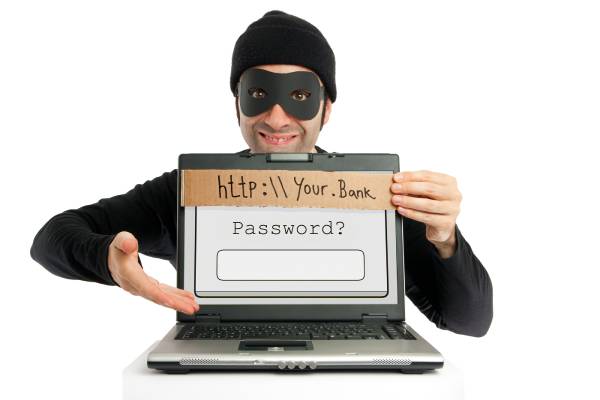
Most broad phishing attempts will try to have you login or share details on a fake page designed to steal your information. For instance, a phisher may pretend to be a popular bank and ask you to login to dispute a charge. If you use that bank, you’ll recognize the fraudulent charge and may act too quickly, clicking their malicious link and typing in your credentials before looking too closely.
Variants like “smishing” or “vishing” are terms people use for attacks that target you via SMS text or through voice communication, like a voicemail or even telephone call.
Spear Phishing
While regular phishing is a broad attack designed to reap rewards through sheer volume, spear phishing is a targeted attack that seeks to get information from a specific person. The main difference with spear phishing is the attacker will use personal details to make you trust them. They’ll refer to you by name, reference your job or even aspects of your life they were able to get through other means like social media.
You don’t need to be rich or famous to be a victim of spear phishing. Often times, criminals looking to attack businesses will spear phish lower-level employees to gain access that allows them to get what they want.
How to Keep Your Passwords Safe from Phishing Attempts
#1 Always Verify Your Contacts
Whether it looks like your boss, your bank, or even a family member messaging you on social media, be alert. Double check the sender’s email to make sure the domain name is correct and not one that simply looks similar.
If it’s on social media, check their profile. Sometimes you’ll click through and realize the person reaching out to you has your family member’s name and profile picture, but it’s a completely different profile than the one you have friended!
#2. Check the Links
Hyperlinks are easily spoofed. Just because the blue text you click on looks right, doesn’t mean the actual URL it brings you to will be the same. This link says www.bing.com but if you click it, you’ll see that it takes you to Google.
If your bank asks you to login, check the link. You can do this on a PC by hovering your cursor over it, or on mobile devices by tapping and holding. Often, you’ll recognize that the link is taking you somewhere very different from where the clickable button suggests.
In some cases, the link may be too long and obscure to verify. Even legitimate businesses use special links that will take you to just the right page, capture some analytics data, or redirect you to a special offer page. But almost every legitimate business will have a way for you to get to these legitimate offers or informational pages without needing to click a special link.
If you’re concerned a link may be malicious, you can always simply use a bookmark to go to the website and login normally then navigate to the correct section. Or you can contact the business or individual sending you the link to verify the link is real. Just make sure to use a phone number you find on an official platform – sometimes phishers include fake phone numbers when they contact you to stop you from discovering their scheme!
#3. Don’t Share Your Password Online
This is a simple one, but an easy one to mistake in the moment. When an official looking email lands in your inbox, or a beloved family member asks for access to your video streaming account, think before you send any information.
No legitimate business will ever need your password outside of when you attempt to login through their website. They can access your details just fine through their internal systems, and they can verify your identify without it. If you still think it’s legitimate, just reach out to them through a different form of communication. If the request was real, they’ll have records of it when you call or speak to them in person.
Remember, handing over one password isn’t always just handing over one password. Like we mentioned above, you’re likely using that password, or a minor variation of it, across multiple accounts on multiple websites. Accidentally leaking your Netflix password can quickly spiral into someone accessing your bank account!
Other Types of Password Attacks
Phishing is just one of the many types of ways that individuals or groups try to get your credentials or access your accounts. It’s one of the most common, and also one of the easier ones to avoid as long as you know what you’re up against.
The other types of account breaching methods employ software, computer networks, or even in-person social engineering to try and get your personal information.

Protect Your Passwords with a 14-Day Free Trial
It’s time to take control of your client passwords. Techferno Password Manager offers beyond-bank security and multiple access levels so you can adapt the tool to how your team works.
Designed for agencies, IT companies and any other business that manages several passwords, Techferno Password Manager allows you to share access to passwords and more while retaining the protection of our state-of-the-art secure platform.
